Passwordless authentication removes the need for traditional passwords by using biometrics, hardware keys, or one-time codes to verify identity. For introverts who process the world with careful attention to friction and cognitive load, the shift away from password management is more than a technical convenience. It aligns with the way many of us prefer to work: quietly, efficiently, and without unnecessary interruption to deep focus.
Most of the conversation around passwordless technology focuses on security metrics and IT adoption rates. What rarely gets discussed is how the psychological texture of authentication affects the people sitting at the keyboard. And for those of us wired to notice friction in our environment, that texture matters more than most people realize.
Our Introvert Strengths and Advantages hub covers a wide range of ways introverts bring genuine value to their work and lives. Passwordless authentication fits naturally into that conversation because it rewards exactly the qualities many introverts already possess: pattern recognition, preference for streamlined systems, and a low tolerance for cognitive clutter.
What Is Passwordless Authentication and Why Does It Matter Now?
Passwordless authentication is exactly what it sounds like: a way to verify who you are without typing a string of characters you are supposed to have memorized. The most common methods include fingerprint or face recognition, hardware security keys, magic links sent to your email, and authenticator apps that generate time-sensitive codes. Some systems combine two of these for added security.
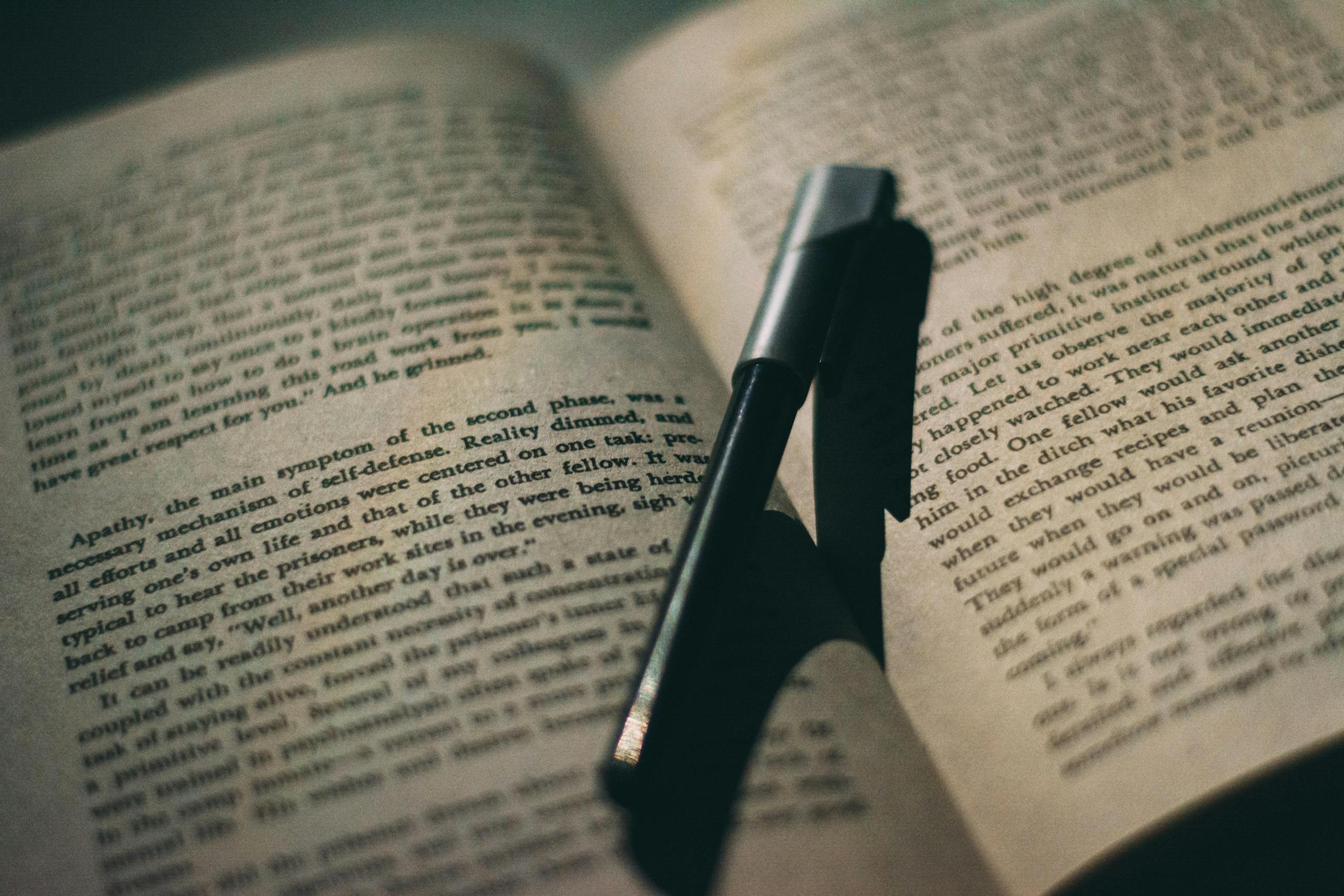
The reason this matters now is partly technical and partly behavioral. Passwords have always been a weak link in security, not because the concept is flawed, but because human beings are not built to manage dozens of unique, complex strings of characters. We reuse them. We write them down. We choose ones that feel memorable, which often means they are predictable. The security community has known this for years, and the shift toward passwordless systems is the industry finally catching up to human psychology.
From a security standpoint, research published through PubMed Central has documented how cognitive load affects decision-making quality. When people are mentally taxed, they take shortcuts. Password fatigue is a real form of cognitive depletion, and the shortcuts it produces create exactly the vulnerabilities that attackers exploit.
Running an advertising agency for over two decades, I watched this play out constantly. My creative teams were brilliant people doing complex, imaginative work. But the moment IT sent another mandatory password reset, I could feel the energy drain out of the room. Not because the request was unreasonable, but because it interrupted the kind of sustained, focused thinking that produces good creative work. For my introverted staff members especially, that interruption cost more than it appeared to on the surface.
How Does Passwordless Authentication Connect to Introvert Cognitive Strengths?
Introverts tend to be deep processors. That is not a personality quirk or a soft observation. It reflects something genuine about how many of us engage with information. We think before we speak. We consider before we act. We notice details that others move past without registering. This cognitive style is a genuine strength, and it is explored in depth in Quiet Power: The Secret Strengths of Introverts, which articulates why this kind of careful, layered thinking produces real advantages in the right environments.
The challenge with deep processing is that it depends on uninterrupted attention. Every time a system demands a password, it pulls focus from wherever that focus was living. For someone who reaches a state of absorbed concentration less easily than an extrovert might, that interruption carries a higher cost. Getting back to the same depth of thought after a disruption takes time and mental energy.
Passwordless systems reduce those interruptions. A fingerprint scan takes less than a second and requires no conscious thought. A hardware key plugged into a USB port becomes invisible after the first few uses. The authentication happens, and the work continues. For people who thrive in sustained focus, that continuity is not a minor convenience. It is a meaningful change in how the workday feels.
I noticed this in myself when my agency started piloting biometric login on our project management systems. The shift was small on paper. In practice, something about the day felt less fragmented. I could move between tasks without the small but persistent tax of credential management interrupting my train of thought. That experience stayed with me, because it pointed to something broader about how system design either supports or undermines the way introverts naturally work.

Does Reduced Friction Actually Improve Introvert Productivity?
Friction in a workflow does not just slow things down. It changes the quality of what gets produced. When a task requires constant small interruptions, the work that emerges tends to be shallower. This is especially true for introverts whose best contributions often come from extended periods of quiet concentration.
Marti Olsen Laney’s foundational work on introversion, which I have referenced many times over the years, explores how introverts process stimulation differently than extroverts. Her insights in The Introvert Advantage helped me understand why certain environmental conditions produce my best thinking and others leave me feeling drained despite putting in the same number of hours. Unnecessary cognitive demands, even small ones, accumulate in ways that compound over a full workday.
Password management is one of those unnecessary demands. It is not intellectually stimulating. It does not produce anything valuable. It simply consumes mental bandwidth that could go toward actual work. Passwordless authentication eliminates that consumption. The result is not dramatic in any single moment, but across a week or a month, the recovered attention adds up to something real.
One of my account directors at the agency was an introvert who consistently produced her best strategic work in the early morning hours before the office filled up. She told me once that she dreaded the weekly IT security checks because they always seemed to hit right when she had found her rhythm. That comment stuck with me. It was not about the inconvenience of the task itself. It was about what the interruption cost her in terms of the mental state she had worked to reach.
What Are the Security Benefits That Introverts Tend to Appreciate Most?
Introverts often have a strong appreciation for systems that work reliably and quietly in the background. We tend not to enjoy calling attention to ourselves, which means we also tend not to enjoy the kind of security theater that requires constant visible action. Passwordless authentication fits this preference well because its strongest protections operate without demanding ongoing user behavior.
Traditional passwords require active maintenance: regular changes, complexity rules, unique credentials for every service. Each of those requirements places the security burden on the user. Passwordless systems shift that burden back to the technology. A FIDO2 hardware key, for example, handles cryptographic verification automatically. The user simply plugs it in. The security is stronger than any password, and the user does not have to think about it.
This alignment between introvert temperament and well-designed systems shows up in other areas too. Laurie Helgoe’s work captured in Introvert Power makes a compelling case for why introverts often excel at building and working within thoughtful structures. Passwordless authentication is, at its core, a more thoughtful structure. It asks less of the person and delivers more protection. That trade is one many introverts will find instinctively appealing.
There is also the phishing dimension. Passwords can be stolen, guessed, or socially engineered. A biometric or hardware-based credential cannot be phished in the same way because it is tied to something physical or biological rather than something stored in memory or written down. For people who prefer to minimize exposure and vulnerability, that characteristic carries genuine appeal beyond the technical specifications.
How Does Passwordless Authentication Support Introvert Work Styles in Professional Settings?
Professional environments have historically been designed around extrovert defaults. Open offices, back-to-back meetings, spontaneous collaboration. Technology has often followed the same pattern, creating systems that demand frequent interaction, confirmation clicks, and visible engagement. Passwordless authentication is one of the first mainstream technology shifts that quietly accommodates a different kind of user.
In sales environments, for example, the ability to move smoothly between client-facing tools without authentication interruptions matters a great deal. Introverts in sales roles often compensate for lower natural energy by being exceptionally prepared and focused. Anything that disrupts that preparation creates a disadvantage. The guidance in How to Be Good at Sales as an Introvert speaks to exactly this dynamic: introverts succeed in sales through depth and preparation, not volume and spontaneity. Systems that protect that depth help.
Beyond sales, consider any role that requires deep analytical work: strategy, research, writing, design, software development. These are fields where introverts are often overrepresented, and where sustained concentration produces the most valuable output. Passwordless authentication removes one more source of fragmentation from those roles.
At my agencies, some of our best strategic thinkers were introverts who needed long uninterrupted stretches to do their best work. I learned early that protecting their focus time was one of the most valuable things I could do as a leader. That meant controlling meeting schedules, yes, but it also meant paying attention to the small operational frictions that accumulated throughout the day. Authentication was one of those frictions. Moving toward simpler, faster verification methods was part of creating an environment where deep thinkers could actually think deeply.
A piece in Frontiers in Psychology examining attention and cognitive performance reinforces what many introverts already sense intuitively: the quality of focused work depends heavily on the conditions surrounding it. System design is part of those conditions, even when it operates below the level of conscious awareness.
Can Passwordless Systems Reduce Workplace Anxiety for Introverts?
Workplace anxiety takes many forms for introverts. Some of it is social. Some of it is environmental. And some of it is the low-grade stress that comes from managing too many systems, too many credentials, and too many opportunities for something to go wrong in a visible way. Forgetting a password at a critical moment, getting locked out of an account during a client presentation, or triggering a security alert because of a failed login attempt: these are small events, but they carry outsized emotional weight for people who tend to internalize stress and prefer not to draw attention to their difficulties.
Passwordless authentication removes most of those specific failure points. You cannot forget your fingerprint. You cannot mistype a biometric. A hardware key either works or it does not, and troubleshooting it does not require calling IT and explaining why you cannot remember the password you set six months ago.
This connects to something I have thought about a lot in the context of introvert purpose and fulfillment. When the small operational stresses of a workday are minimized, more energy becomes available for the work that actually matters. The Powerful Purpose of Introverts explores how introverts often find their deepest satisfaction in meaningful, substantive contribution. That kind of contribution requires a certain quality of mental and emotional presence. Reducing background anxiety, even through something as mundane as authentication design, supports that presence.
I spent a significant portion of my career managing my own anxiety in professional settings. As an INTJ, I was good at appearing composed while internally cataloging every potential problem. Password management was never a major source of stress for me personally, but I watched it become one for people on my team, particularly those who were already managing a high cognitive load. The relief that came with simpler authentication was visible in their behavior, even if they would not have described it in those terms.

What Does the Introvert Preference for Depth Tell Us About System Design?
There is a broader conversation embedded in the specific topic of passwordless authentication. It is a conversation about how technology systems either accommodate or resist the way introverts naturally operate. Most enterprise technology was not designed with introvert cognitive styles in mind. It was designed for speed, visibility, and constant interaction. The introvert experience of those systems is often one of friction, overstimulation, and interruption.
Passwordless authentication is one example of a design choice that happens to align well with introvert needs, even though that was not the primary intention. The designers were thinking about security and user convenience. The introvert benefit is a byproduct. That byproduct is worth naming explicitly, because it points toward what better system design could look like more broadly.
Susan Cain’s TED Talk brought introvert strengths into mainstream awareness in a way that few other cultural moments have managed. The conversation it sparked, captured in The Power of Introverts TED Talk, helped many people articulate something they had sensed but never had language for: that the environments and systems around us are often calibrated for a different kind of person. Passwordless authentication, modest as it is, represents a small correction in that calibration.
When I think about the Fortune 500 clients my agencies served over the years, many of them were running internal technology that created constant low-level friction for their employees. The cumulative cost of that friction, in lost focus, increased stress, and reduced output quality, was rarely measured because it was invisible. It showed up in turnover rates and employee satisfaction scores, but the connection to system design was rarely drawn. Passwordless authentication gives us a concrete example of how small design improvements can have real human effects.
How Should Introverts Think About Adopting Passwordless Authentication?
Adopting passwordless authentication is not complicated, but it does require a bit of intentional setup. The most accessible starting point for most people is enabling biometric login on devices that already support it. Most modern smartphones and laptops have fingerprint or face recognition built in. Turning it on for your most-used accounts takes minutes and delivers immediate benefits.
For people who want stronger security, a hardware security key is worth considering. These small devices, which typically cost between thirty and sixty dollars, provide some of the strongest authentication available. They work with most major platforms and services. The initial setup requires some attention to detail, which is something many introverts handle well. Once configured, the key becomes part of a routine that requires no ongoing thought.
Authenticator apps occupy a middle ground. They require a phone to be present, which adds a small dependency, but they eliminate the need to remember passwords for the accounts they protect. For someone managing a large number of professional accounts, an authenticator app combined with a password manager can significantly reduce the cognitive overhead of credential management while the industry continues its broader shift toward fully passwordless systems.
The Psychology Today piece on why deeper conversations matter makes a point that applies here in an indirect but real way: introverts invest their energy deliberately, and they notice when that energy is being consumed by things that do not deserve it. Password management is one of those things. Setting up passwordless authentication is a one-time investment that returns attention and focus for as long as the system is in use.
From a professional standpoint, advocating for passwordless systems within your organization is also worth considering. If you are in a position to influence technology decisions, the case is strong on both security and productivity grounds. The Harvard Program on Negotiation’s perspective on introverts is a useful reminder that introverts often succeed in advocacy and influence through preparation and evidence rather than volume and persistence. The evidence for passwordless authentication is solid, and making that case quietly and thoroughly is exactly the kind of contribution introverts tend to make well.
What Does the Future of Authentication Look Like for Introverts?
The direction of authentication technology is clearly toward less friction and more passive verification. Behavioral biometrics, which analyze typing patterns, mouse movements, and device handling to continuously verify identity, represent the next step. These systems work entirely in the background. The user does nothing. The verification happens invisibly, continuously, and without interruption.
For introverts who value uninterrupted focus, that trajectory is genuinely encouraging. The authentication experience of the future may be one where the system simply knows who you are and stays out of your way. That is a design philosophy that aligns naturally with how many introverts prefer to work: with capable systems handling the background operations while human attention goes toward the work that actually requires it.
There are legitimate questions about privacy and data collection that come with behavioral biometrics, and those deserve careful consideration. The same attention to nuance that makes introverts good at deep work also makes many of us thoughtful about the implications of new technologies. That thoughtfulness is an asset in evaluating these systems, not a reason to avoid them entirely.
Additional perspectives on how cognitive styles interact with technology and professional environments are worth exploring. PubMed Central’s research on attention and cognitive performance provides useful context for understanding why the conditions surrounding focused work matter as much as the work itself. And Rasmussen University’s guidance on marketing for introverts illustrates how introverts in client-facing roles benefit specifically from tools and systems that reduce operational friction.
What I find most interesting about this moment in authentication technology is that the industry arrived at passwordless solutions through a security lens, not a human-centered design lens. Yet the human benefits, particularly for people who process deeply and prefer low-friction environments, are substantial. That convergence feels worth paying attention to. It suggests that when technology is designed to work better for everyone, it often ends up working especially well for introverts.

If you want to explore more about how introvert strengths show up in unexpected places, the complete Introvert Strengths and Advantages hub covers the full range of ways introverts bring genuine value to their work, relationships, and daily lives.
About the Author
Keith Lacy is an introvert who’s learned to embrace his true self later in life. After 20 years in advertising and marketing leadership, including running agencies and managing Fortune 500 accounts, Keith now channels his experience into helping fellow introverts understand their strengths and build fulfilling careers. As an INTJ, he brings analytical depth and authentic perspective to every article, drawing from both professional expertise and personal growth.
Frequently Asked Questions
What is passwordless authentication in simple terms?
Passwordless authentication is a way to verify your identity without typing a password. Instead, it uses something you are, such as a fingerprint or face scan, something you have, such as a hardware security key or your phone, or a one-time code sent to a verified device. The result is faster, more secure access that does not depend on memorizing or managing complex character strings.
Why might introverts specifically benefit from passwordless authentication?
Introverts often work best in states of sustained, uninterrupted focus. Password prompts, mandatory resets, and credential management create small but real interruptions to that focus. Passwordless systems reduce those interruptions significantly, allowing deep thinkers to maintain concentration for longer periods. There is also a reduction in low-grade anxiety associated with forgotten passwords, account lockouts, and visible authentication failures in professional settings.
Is passwordless authentication actually more secure than traditional passwords?
In most implementations, yes. Hardware-based passwordless credentials, such as FIDO2 keys, use cryptographic verification that cannot be phished or guessed. Biometrics are tied to physical characteristics rather than stored strings that can be stolen from a database. The main security considerations involve the backup and recovery processes, which should be set up carefully. When implemented well, passwordless authentication eliminates the most common attack vectors that traditional passwords face.
How do I get started with passwordless authentication?
The easiest starting point is enabling biometric login on devices you already own. Most modern smartphones and laptops support fingerprint or face recognition, and major accounts including Google, Apple, and Microsoft now support passkeys that use these biometrics. For stronger security, a hardware key such as a YubiKey is worth the modest investment. Setup typically takes less than an hour and the ongoing experience requires no active management once configured.
Does passwordless authentication work across all platforms and services?
Adoption is widespread and growing. Most major platforms including Google, Microsoft, Apple, GitHub, and many financial institutions now support passkeys or hardware key authentication. Smaller services and older enterprise systems may still require traditional passwords, which is why a password manager remains useful during the transition period. The industry standard FIDO2 protocol has broad support, and the trend toward universal passwordless compatibility is accelerating as more organizations recognize both the security and usability benefits.