Gmail’s authentication changes are reshaping how emails get delivered, verified, and trusted across the internet. If you send emails regularly, whether for a newsletter, a small business, or personal communication, these updates affect whether your messages actually reach people’s inboxes.
Google has implemented stricter sender requirements around email authentication protocols, specifically SPF, DKIM, and DMARC. Understanding what these changes mean in practical terms, and how to respond to them thoughtfully, matters more now than it did even a year ago.
I want to be honest with you: this is not the kind of topic I ever imagined writing about on Ordinary Introvert. But as someone who spent two decades running advertising agencies and managing digital communications at scale, I’ve watched technology shifts like this one create quiet chaos for people who weren’t paying attention. And I’ve noticed something interesting about how introverts specifically tend to respond to these kinds of changes, which is worth exploring.
Major technological shifts like this one sit squarely in the territory of life transitions, the kind that arrive without fanfare and demand a response. Our Life Transitions and Major Changes hub covers the full range of how introverts process and respond to change, and the quiet disruption of email authentication fits that pattern more than you might expect.

What Are Gmail’s Authentication Changes and Why Did Google Make Them?
Google began rolling out stricter email authentication requirements in early 2024, targeting senders who send large volumes of email to Gmail accounts. The core changes center on three technical standards that have existed for years but were never strictly enforced: SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance).
What’s your personality type?
Take our free 40-question assessment and get a detailed personality profile with dimension breakdowns, context analysis, and personalised insights.
Discover Your Type8-12 minutes · 40 questions · Free
SPF tells receiving mail servers which IP addresses are authorized to send email on behalf of your domain. DKIM adds a cryptographic signature to your emails that proves the message wasn’t tampered with in transit. DMARC ties the two together and tells receiving servers what to do when an email fails authentication, whether to reject it, quarantine it, or let it through anyway.
Google’s stated reason for the change is straightforward: spam, phishing, and email spoofing have become significant problems at scale. By requiring proper authentication, Google makes it harder for bad actors to impersonate legitimate senders. That’s genuinely good for everyone. The complication is that many small senders, newsletters, nonprofits, solo entrepreneurs, and anyone who set up email years ago without thinking about these standards, suddenly found themselves scrambling.
At my agencies, we managed email campaigns for Fortune 500 brands where deliverability was tracked obsessively. I had team members whose entire job was monitoring inbox placement rates. But most people running a small newsletter or a modest business email list don’t have that infrastructure. The Gmail authentication changes hit them differently, and the response required is often more disorienting than the technical problem itself.
Who Does This Actually Affect?
Google’s requirements apply most strictly to bulk senders, defined as anyone sending 5,000 or more messages per day to Gmail accounts. If you’re in that category, you already needed SPF, DKIM, and DMARC configured, and you needed a one-click unsubscribe option in your emails.
For smaller senders, the requirements are less rigid, but the underlying principle still applies. Google’s spam filters have become more sophisticated, and emails that lack proper authentication are increasingly likely to land in spam folders or be rejected entirely, regardless of volume. Even if you send fifty emails a week from a custom domain, misconfigured authentication can quietly undermine your deliverability without any obvious error message telling you what went wrong.
This quiet, invisible failure is something I’ve thought about a lot in relation to how introverts process technical problems. Many of us prefer to work things out internally before asking for help. We notice something is off, we research it, we sit with the complexity. That approach works well for a lot of challenges. With email authentication, though, the invisible nature of the problem means you might not realize your messages are being filtered for weeks or months.
There’s an interesting parallel in how highly sensitive people handle unexpected disruptions. Managing major changes as an HSP often involves that same slow-burn awareness, noticing something feels off before you can name exactly what it is, then needing time and space to process the full picture before responding. Email authentication issues have that same quality of creeping disruption.

How Do You Check Whether Your Email Is Properly Authenticated?
Checking your authentication status is more accessible than the technical jargon suggests. Several free tools let you verify whether your SPF, DKIM, and DMARC records are correctly configured. MXToolbox is one of the most widely used. Google’s own Postmaster Tools provides deliverability data if you send enough volume to generate meaningful reporting.
The process typically works like this: you enter your domain name into a lookup tool, and it checks your DNS records to see whether your SPF record exists and is properly formatted, whether DKIM is configured for your sending domain, and whether you have a DMARC policy in place. Each check returns a result that tells you what’s working and what needs attention.
One thing I learned from years of managing email campaigns is that the technical setup is usually less complicated than it sounds, but it does require access to your domain’s DNS settings. If you’re using a service like Mailchimp, ConvertKit, or similar platforms, they often provide authentication setup guides specific to their service. Many have simplified this process considerably in response to the Gmail changes.
Where people get stuck is in the gap between understanding what needs to be done and actually doing it. That gap is where anxiety lives. And for introverts who process deeply before acting, that gap can stretch into weeks of reading, researching, and circling the problem without quite landing on a solution. Recognizing that pattern in yourself is genuinely useful information.
Adam Grant’s work on introverted leadership at Wharton touches on something relevant here. Grant’s research on introverts in professional environments suggests that introverted people often outperform in situations requiring careful preparation and deep thinking, which is exactly the kind of thinking that technical problem-solving demands. The challenge is moving from preparation into action without letting the research phase become a form of avoidance.
What Does SPF Actually Do and How Do You Set It Up?
SPF is a DNS record that lists the mail servers authorized to send email from your domain. When someone receives an email claiming to be from your domain, their mail server checks your SPF record to verify the sending server is on your approved list. If it isn’t, the email may be flagged as suspicious.
Setting up an SPF record means adding a TXT record to your domain’s DNS settings. The record looks something like this: v=spf1 include:mailservice.com ~all. The include portion references your email service provider’s SPF record, and the ~all at the end tells receiving servers to apply a soft fail if the sending server isn’t listed. A hard fail uses -all instead, which is stricter.
One important constraint: you can only have one SPF record per domain. If you use multiple email services, you need to combine them into a single record rather than creating separate records for each. Creating multiple SPF records breaks authentication in ways that aren’t always immediately obvious, and I’ve seen this mistake trip up even technically competent teams.
During one campaign I ran for a retail client about fifteen years ago, we discovered mid-campaign that their IT team had added a second SPF record when they switched marketing platforms, without removing the original. Deliverability dropped significantly before anyone connected the cause. It took three days of troubleshooting to find a two-line DNS entry as the culprit. That experience made me deeply respectful of how small configuration errors can have outsized consequences.

What Is DKIM and Why Does the Cryptographic Signature Matter?
DKIM works differently from SPF. Rather than checking where an email came from, DKIM verifies that the email’s content hasn’t been altered between sending and receiving. Your email service generates a private key that signs outgoing messages, and a corresponding public key stored in your DNS records allows receiving servers to verify that signature.
The practical value of DKIM is that it creates a verifiable chain of custody for your emails. A message signed with your DKIM key can be proven to have originated from your authorized sending service and to have arrived intact. Without DKIM, there’s no cryptographic proof that an email claiming to be from you actually is.
Most major email service providers handle DKIM setup by giving you a specific DNS record to add to your domain. The record contains your public key and is usually a long string of characters that looks intimidating but simply needs to be copied accurately into your DNS settings. The error that most commonly causes DKIM failures is truncation, where the record gets cut off during copy-paste or where a hosting provider’s DNS interface has character limits that aren’t immediately visible.
There’s something worth noting about how introverts tend to approach technical documentation. Many of us read instructions thoroughly, sometimes more thoroughly than necessary, before taking action. That thoroughness is an asset when setting up DKIM because the details genuinely matter. Copying a key incorrectly, even by one character, breaks the entire verification chain. The careful, methodical approach that sometimes gets labeled as overthinking is actually exactly right for this kind of task.
This connects to something I’ve observed about introverts who are considering major career transitions into fields that require technical precision. Certain academic paths cultivate exactly this kind of careful, detail-oriented thinking, and it translates well into technical problem-solving later in life.
How Does DMARC Bring Everything Together?
DMARC is the policy layer that sits on top of SPF and DKIM. It tells receiving mail servers what to do when an email fails authentication checks, and it enables reporting so you can see who is sending email on behalf of your domain.
A DMARC policy has three possible settings. A policy of none means you’re monitoring but not taking action on failures. Quarantine means suspicious emails go to the spam folder. Reject means they’re blocked entirely. Google’s requirements for bulk senders specify that you need at least a DMARC policy of none in place, meaning you need to have the record configured even if you’re not yet enforcing strict rejection.
The reporting component of DMARC is genuinely valuable. When you configure a DMARC record with a reporting email address, you receive aggregate reports showing which servers are sending email from your domain, how many messages passed or failed authentication, and from which IP addresses. This visibility is something many small senders have never had before.
At one agency I ran, we started requiring DMARC reporting for all client email programs around 2016, before it was widely discussed. The reports revealed that several clients had forgotten about old email systems still sending on their behalf, including one client whose previous marketing platform was still sending automated messages years after they’d switched providers. DMARC reporting made that visible in a way nothing else would have.
For introverts who value having complete information before making decisions, DMARC reporting offers something genuinely useful: a comprehensive picture of your email ecosystem. You can see the full scope of the problem before deciding how to respond. That kind of informed decision-making plays to our strengths.
What Happens If You Ignore These Changes?
The consequences of ignoring Gmail’s authentication requirements range from mildly inconvenient to seriously damaging, depending on how you use email. For bulk senders who haven’t complied, Google has indicated that non-compliant messages will be rejected. That means your emails don’t reach their destination, and the people you’re trying to reach have no idea why they stopped hearing from you.
For smaller senders, the impact is subtler but still real. Emails without proper authentication are more likely to be filtered into spam, where most people never look. Your open rates drop, your engagement drops, and you may not connect the cause to the effect for months. The relationship you’ve built with your audience quietly erodes.
There’s also a reputational dimension. Domain reputation is a real factor in email deliverability, and persistent authentication failures can damage your domain’s standing with email providers over time. Rebuilding that reputation requires consistent authenticated sending over an extended period. Prevention is considerably easier than recovery.
What strikes me about this situation is how it mirrors other forms of gradual drift that introverts sometimes experience in professional contexts. You’re not aware anything is wrong because there’s no dramatic signal, just a slow erosion of connection. The importance of maintaining genuine connection applies as much to email relationships as to personal ones, and neglecting the infrastructure that supports those connections has real costs.

How Should Introverts Approach This Kind of Technical Transition?
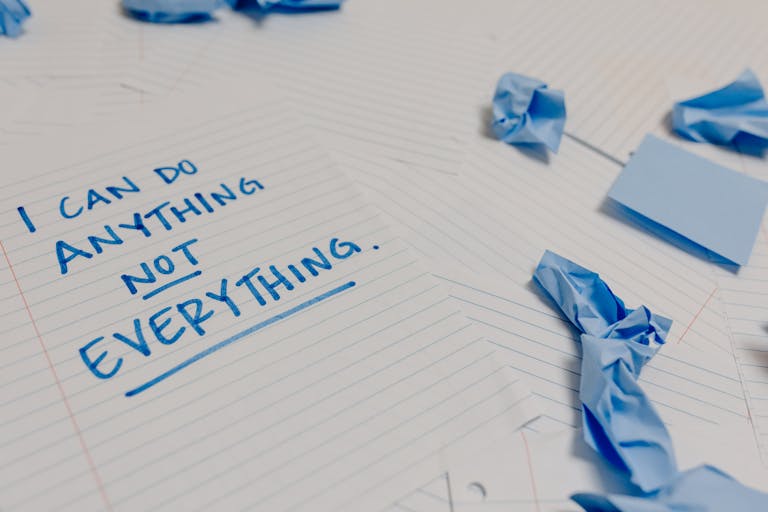
There’s a pattern I’ve noticed in myself and in introverts I’ve worked with: we tend to respond to technical disruptions by going deep before going wide. We read everything, understand the underlying mechanisms, and build a mental model of the problem before we act. That approach has genuine value, but it can also become a way of deferring action indefinitely.
With Gmail authentication changes, the action required is finite and specific. You need to check whether your SPF, DKIM, and DMARC records are correctly configured. If they’re not, you need to fix them, either by following your email provider’s documentation or by working with whoever manages your domain’s DNS settings. That’s the complete scope of the task.
What I’d suggest is treating this the way I’ve learned to treat other technical decisions in a business context: define the minimum viable outcome, take the first concrete step, then reassess. The minimum viable outcome here is having all three authentication records correctly configured. The first step is running a check on your current setup using a free tool. Everything else follows from what that check reveals.
Solo work, including solo problem-solving, is something many introverts genuinely excel at when given the space to work methodically. The same self-reliance that makes solo travel feel freeing rather than isolating applies to working through technical challenges independently. You don’t need to crowd-source this decision or wait for someone else to tell you what to do. The information is available, and your natural inclination toward thorough research is an advantage.
That said, knowing when to ask for help matters too. If you’ve read the documentation, run the checks, and still can’t determine what’s wrong, bringing in someone with specific DNS expertise is a reasonable choice, not a failure. Recognizing the limits of productive solo work is its own form of self-awareness.
What About Email Platforms and Third-Party Senders?
If you use a dedicated email service provider, the authentication setup process is usually guided and well-documented. Platforms like Mailchimp, ConvertKit, ActiveCampaign, and similar services have responded to the Gmail changes by updating their onboarding flows and creating specific authentication setup guides. Many now flag authentication status directly in their dashboards.
The complication arises when you use multiple services that send email on your behalf. Your newsletter platform, your CRM, your transactional email service for order confirmations, your customer support platform, all of these may be sending email from your domain. Each one needs to be included in your SPF record, and each one may require its own DKIM setup.
Mapping out all the services sending email from your domain before you start making changes is genuinely important. I’ve seen organizations configure authentication for their primary email platform and consider the job done, only to discover weeks later that their transactional emails or support tickets were still failing authentication because those systems weren’t included in the original setup.
There’s a broader principle here that I think applies well beyond email. When you’re facing a systemic change that touches multiple parts of your infrastructure, whether technical or organizational, understanding the full scope before you act prevents the kind of partial solutions that create new problems. That comprehensive thinking is something introverts tend to do naturally, and it’s worth trusting in situations like this one.
The instinct to map the complete landscape before taking action is something I’ve seen play out well in academic settings too. Environments that reward depth of thinking over speed of response tend to produce people who are genuinely good at this kind of systematic problem-solving. That’s a real professional advantage when technical transitions demand careful, comprehensive responses.
How Does This Connect to Broader Patterns of Change Resistance?
I want to step back from the technical details for a moment, because there’s something more interesting happening here than DNS records and cryptographic signatures.
Many introverts have a complicated relationship with externally imposed change. We’re often quite comfortable with change we initiate ourselves, because we’ve had time to think it through, build a mental model, and decide it’s the right direction. Change that arrives from outside, particularly change with technical complexity and unclear timelines, tends to activate a different response. There’s resistance, not necessarily because the change is bad, but because it hasn’t been processed yet.
Gmail’s authentication requirements are a good example of this. The changes themselves are reasonable. Better email authentication reduces spam and phishing. Most people, once they understand what’s being asked of them, don’t object to the underlying goal. The friction is in the transition, in the gap between “this change has happened” and “I understand what it means and what I need to do.”
There’s a concept in psychology around the difference between change resistance and change processing. What looks like resistance is often just the time required to genuinely absorb and integrate new information before acting. Some psychological frameworks suggest that people who process information more deeply before acting tend to make more durable changes once they do act, because the decision is more fully integrated rather than reactive.
The anime series “Tsubame Wants to Change” captures something of this tension in a different context. Tsubame’s internal struggle with change resonates with many introverts precisely because the desire to change and the difficulty of initiating that change coexist in ways that feel genuinely familiar. Technical transitions like Gmail authentication updates can activate that same internal dynamic.
What I’ve found useful, both in my agency work and in my personal life, is distinguishing between the processing phase and the action phase. Giving yourself explicit permission to spend a defined amount of time understanding the problem fully, and then committing to a specific action step at the end of that period, tends to work better than either rushing into action before you’re ready or staying in the research phase indefinitely.
What Are the Practical Steps to Get Compliant?
Getting your email authentication in order is a concrete, completable task. Here’s how I’d approach it if I were starting from scratch.
Start by auditing what you have. Use a tool like MXToolbox or Google’s Admin Toolbox to check your current SPF, DKIM, and DMARC records. Note what’s present, what’s missing, and what’s misconfigured. This audit takes about fifteen minutes and gives you a clear picture of your starting point.
Next, identify all the services sending email from your domain. Go through your accounts and make a list: your primary email provider, your newsletter platform, any CRM or marketing automation tools, your transactional email service, your customer support platform. Each of these needs to be represented in your authentication setup.
Then work through the setup for each protocol. SPF first, since it’s the foundation. Add or update your SPF TXT record to include all your sending services. DKIM next, following the specific setup instructions from each email service you use. DMARC last, starting with a policy of none and a reporting address so you can monitor results before enforcing stricter policies.
After making changes, verify them. Run the same audit tools again to confirm everything is reading correctly. DNS changes can take up to 48 hours to propagate fully, so wait before concluding something isn’t working.
Finally, monitor your DMARC reports over the following weeks. The aggregate reports will show you whether your authentication is working as expected and whether any unauthorized senders are using your domain. Adjust your DMARC policy toward quarantine or reject once you’re confident your legitimate email is all passing authentication correctly.
One resource worth noting: approaches to marketing that work well for introverts often emphasize building genuine, sustainable systems rather than high-volume, high-noise tactics. Proper email authentication is part of building a sustainable email presence, one where the messages you do send are reliably delivered and trusted.

What Does This Mean for Your Relationship With Email Going Forward?
Email remains one of the most direct, personal forms of digital communication available. Unlike social media, where algorithmic filtering determines who sees what, email sent to someone’s inbox is a direct line of communication. That directness is something many introverts genuinely value, because it allows for depth and substance rather than the surface-level exchange that social platforms tend to reward.
Gmail’s authentication changes are, in a meaningful sense, an investment in preserving that directness. By making authenticated email more trustworthy and filtering out unauthenticated messages more aggressively, Google is creating conditions where properly configured email has more signal value. Your authenticated messages stand out more in a landscape where unauthenticated messages are increasingly filtered.
That framing matters to me. When I was running agencies, I always told clients that the goal of email wasn’t volume, it was connection. Sending fewer, better, more reliably delivered messages to people who actually wanted to hear from you was always more valuable than sending large volumes of messages that landed in spam. The Gmail changes push the entire ecosystem in that direction.
For introverts who tend to prefer depth over breadth in their communications, this is genuinely good news. The technical overhead of proper authentication is a one-time investment that pays ongoing dividends in deliverability and trust. Once your authentication is correctly configured, you can focus on what you actually want to say rather than worrying about whether your messages are reaching anyone.
There’s also something worth acknowledging about the broader context of how we handle institutional change. Some research on adaptive responses to environmental change suggests that people who can distinguish between changes requiring resistance and changes requiring adaptation tend to have better outcomes across a range of domains. Gmail’s authentication requirements fall clearly into the adaptation category. The change is happening regardless of how any individual feels about it, and the question is simply how to respond effectively.
That capacity for clear-eyed assessment, separating what can be changed from what can’t, and directing energy accordingly, is something introverts often develop through years of working in environments that weren’t designed for us. It turns out to be a genuinely useful skill when handling technological transitions too.
If you’re working through other major shifts in how you operate, whether personal or professional, the Life Transitions and Major Changes hub has resources specifically oriented toward how introverts process and respond to change across different contexts.
About the Author
Keith Lacy is an introvert who’s learned to embrace his true self later in life. After 20 years in advertising and marketing leadership, including running agencies and managing Fortune 500 accounts, Keith now channels his experience into helping fellow introverts understand their strengths and build fulfilling careers. As an INTJ, he brings analytical depth and authentic perspective to every article, drawing from both professional expertise and personal growth.
Frequently Asked Questions
Do Gmail’s authentication changes affect personal Gmail accounts or only business email?
Gmail’s authentication requirements primarily target senders using custom domains, meaning businesses, newsletters, and anyone sending from an address like name@yourdomain.com. Personal Gmail accounts (name@gmail.com) are not affected by these requirements in terms of setup, since Google manages authentication for Gmail accounts directly. If you send email from a custom domain, even for personal or small-scale use, proper SPF, DKIM, and DMARC configuration improves your deliverability regardless of your sending volume.
What happens to emails that fail Gmail’s authentication checks?
Emails that fail authentication checks face several possible outcomes depending on the sending volume and the severity of the failure. For bulk senders who don’t meet Google’s requirements, messages may be rejected outright, meaning they never reach the recipient. For smaller senders or partial authentication failures, messages are more likely to be filtered into the spam folder. In either case, the recipient typically has no notification that a message was expected and didn’t arrive, which makes authentication failures particularly damaging to ongoing communication relationships.
How long does it take to set up proper email authentication?
For most small senders using a single email platform, the setup process can be completed in one to three hours, including the time needed to read your email provider’s documentation, access your domain’s DNS settings, add or update the necessary records, and verify that everything is working correctly. DNS changes can take up to 48 hours to propagate fully across the internet, so you may need to wait before your verification checks show the updated records. Organizations using multiple email services may need additional time to audit all their sending systems and ensure each is properly included in their authentication setup.
Is DMARC required or just recommended?
For bulk senders (those sending 5,000 or more messages per day to Gmail accounts), Google requires a DMARC record to be in place. A policy of none is acceptable to meet the minimum requirement, meaning you don’t have to enforce strict rejection of failing messages immediately. For smaller senders, DMARC is not explicitly required by Google’s current policies, but having it in place is strongly advisable. DMARC provides visibility into who is sending email from your domain, protects against spoofing, and positions you well as email authentication standards continue to tighten across the industry.
Can you fix email authentication problems without technical expertise?
Many people without technical backgrounds successfully configure email authentication by following the step-by-step documentation provided by their email service providers. The process requires access to your domain’s DNS settings, which is typically available through your domain registrar or hosting provider’s control panel. The steps themselves involve copying specific text values into specific fields, which is more about careful attention to detail than technical knowledge. That said, if you encounter errors or your domain is hosted through a provider with an unfamiliar interface, reaching out to your email platform’s support team or a freelance DNS specialist is a reasonable option. The investment in getting it right is worthwhile given the ongoing deliverability impact.